CABEM Assessment & Risk Manager
Risk Manager – Software Overview.
The CABEM Assessment & Risk Manager
This decade has seen a massive leap in dependency on third-party vendors. With that has come news-worthy vendor security holes disrupting operations and damaging reputations.
Yet, some organizations still have no way to assess technology and security risks. Others depend on point-in-time due diligence processes that are tedious and not nearly effective enough. We have a better approach.

92% of legal and compliance leaders say point-in-time due diligence processes could not have identified risks that had a material impact on their businesses. – Gartner Research
CABEM’s iterative approach to third-party risk management provides everything you need to:
• Assess, track, and compare vendors as their security postures evolve
• Help preferred vendors remediate risk and improve their standing
• Maintain and prove regulatory compliance
• House and adaptively assess industry standard, and custom, requirements
Those businesses that employ the iterative approach indicate business partners are 3.5X more satisfied with the business’s ability to quickly engage with third parties, 2X as satisfied with their ability to remediate third-party risks before they have a potential impact, and 1.5X more satisfied with the ability to surface third-party risks before they are too late to remediate. – Gartner Research
Here’s How It Works:
- Create – Leverage assessment surveys or create your own
- Invite – Send vendors a secure link to complete the assessment online
- Score – Configure automated scoring and acceptance thresholds
- Inform – Surface opportunities for vendors to improve
- Decide – Compare vendors side-by-side for more informed decisions
- Report – Instantly output audit-ready reports
- Repeat – Invite vendors to return frequently, confirm past answers, and provide updates
- Protect your brand reputation
- Ensure regulatory compliance
- Maintain operational stability
CABEM has 21+ years of experience developing custom enterprise solutions for highly-regulated industries. We created the CABEM Third-Party Risk Assessment platform in collaboration with top experts in enterprise risk and following our motto:
Software should be able to do business the way you want to, so that’s how we build it.
What is a Vendor Risk Assessment?
An organization should not engage with a third-party vendor until they have performed an evaluation of their potential risks, a vendor risk assessment. Once an assessment has been completed and approved, then the third-party vendor relationship can move forward. Regular assessments help to maintain business standards and provide visibility into vendor security. The assessment identifies hidden risks that otherwise may have been overlooked during vendor onboarding. The types of vendor risks include those related to compliance, reputation, finances, operations, and strategy, as well as an organization’s cybersecurity.
What is CABEM Assessment & Risk Manager?
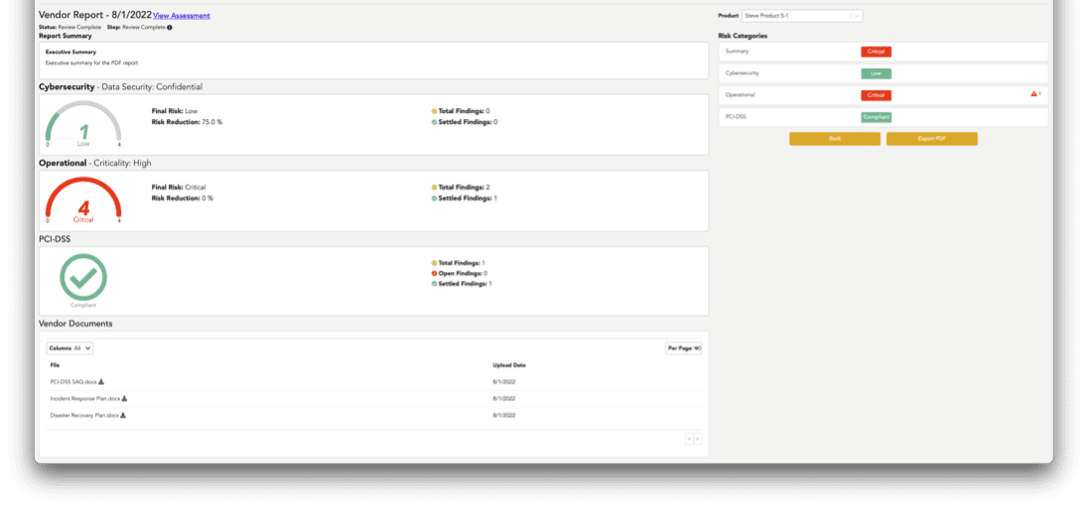
A tool to help facilitate this assessment and manage the process of evaluating the vendor’s risk as seamlessly as possible. By covering topics such as CMMC, SOC, PCI, PII, HIPPA, and CJIS, for example, the process of evaluating the Vendor can not only be efficient but the results can be easily reported to the Vendor as well as Auditors and internal stakeholders.
Vendor Assessment & Risk Management – 4-Step Process
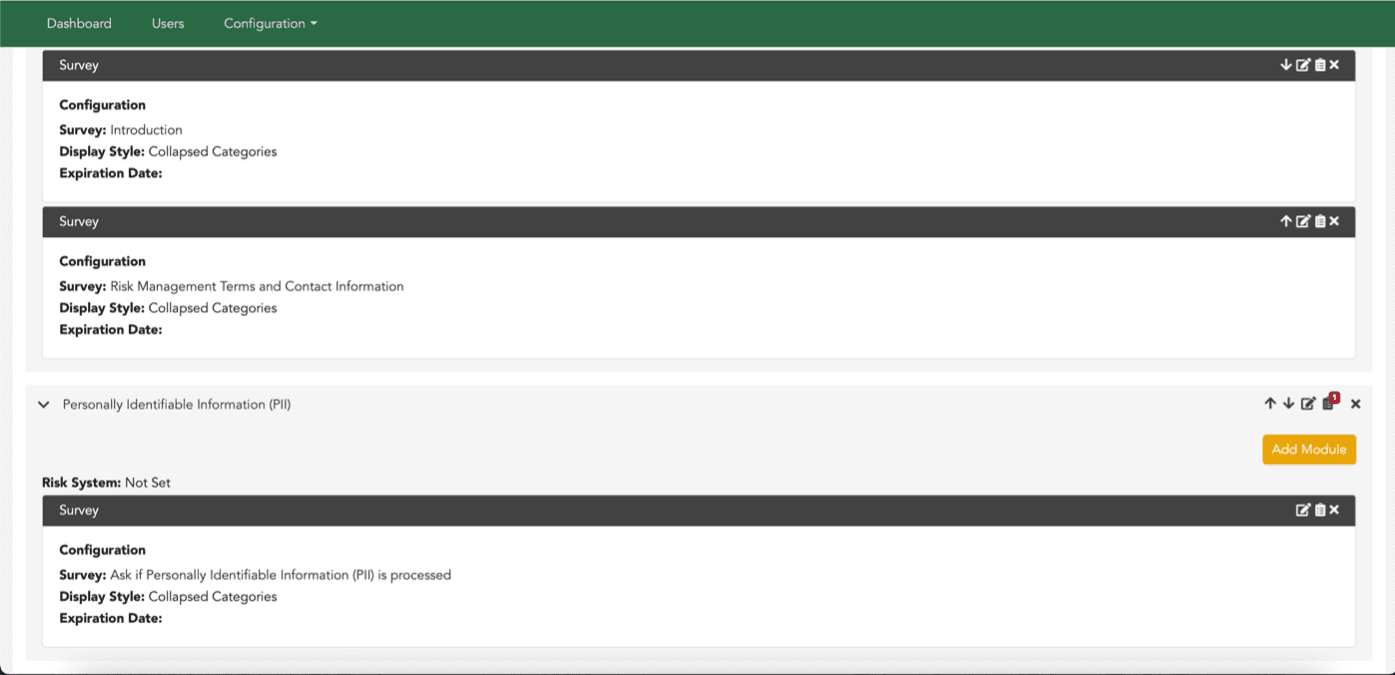
1. Configure your questions – enter questions directly or import your existing spreadsheet of questions into a highly configurable questions engine
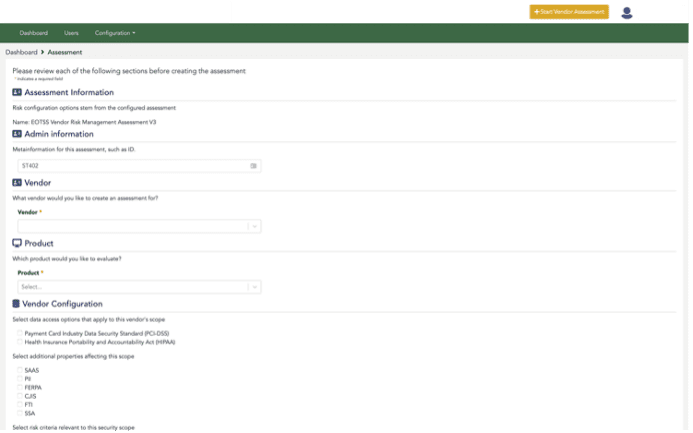
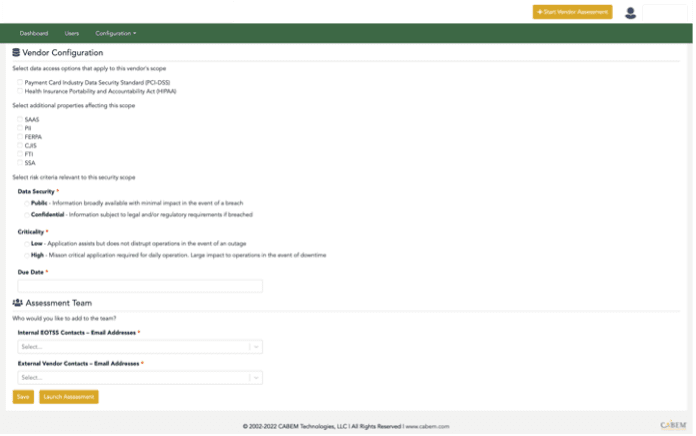
2. Launch the Assessment – identify who needs to complete the assessment, select the security topics to be assessed and configure the criticality and the security level of the assessment.
3. Vendor Assessment Completion – the Vendor Assessment is then completed by Vendors as assigned. They log into the Vendor Portal so all information is captured in your system for easy access and reporting.
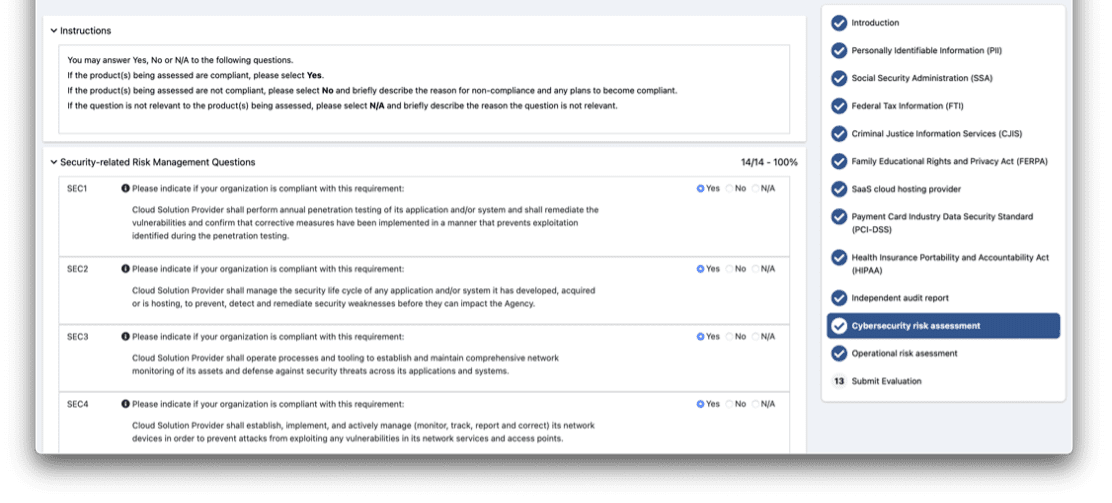
4. Report on the Vendor Assessment and evaluate risk mitigation steps needed.
Integrate or Unite to Build Better
At our core we are a custom software company. We are comfortable addressing any unique technical requirements a customer may have, including integrations between systems.
We can tailor fit the product to any needs of the customer. Current integrations include HRIS systems, SSO, Active Directory, Primary Source Verification, DocuSign, and multiple training platforms.
Headquarters
2000 Commonwealth Avenue
Suite #215
Auburndale, MA 02466
Cybersecurity Services
3270 Blazer Pkwy Suite #101
Lexington, KY 40509
